PrerequisitesDocumentation Index
Fetch the complete documentation index at: https://docs.truu.ai/llms.txt
Use this file to discover all available pages before exploring further.
- Enable the FIDO2 Security Keys authentication method in Azure AD
- Configure FIDO2 security key settings
- Network / Firewall requirements
- Windows 11 2004 24H1 or above
Enable FIDO2 Security Keys in Entra ID
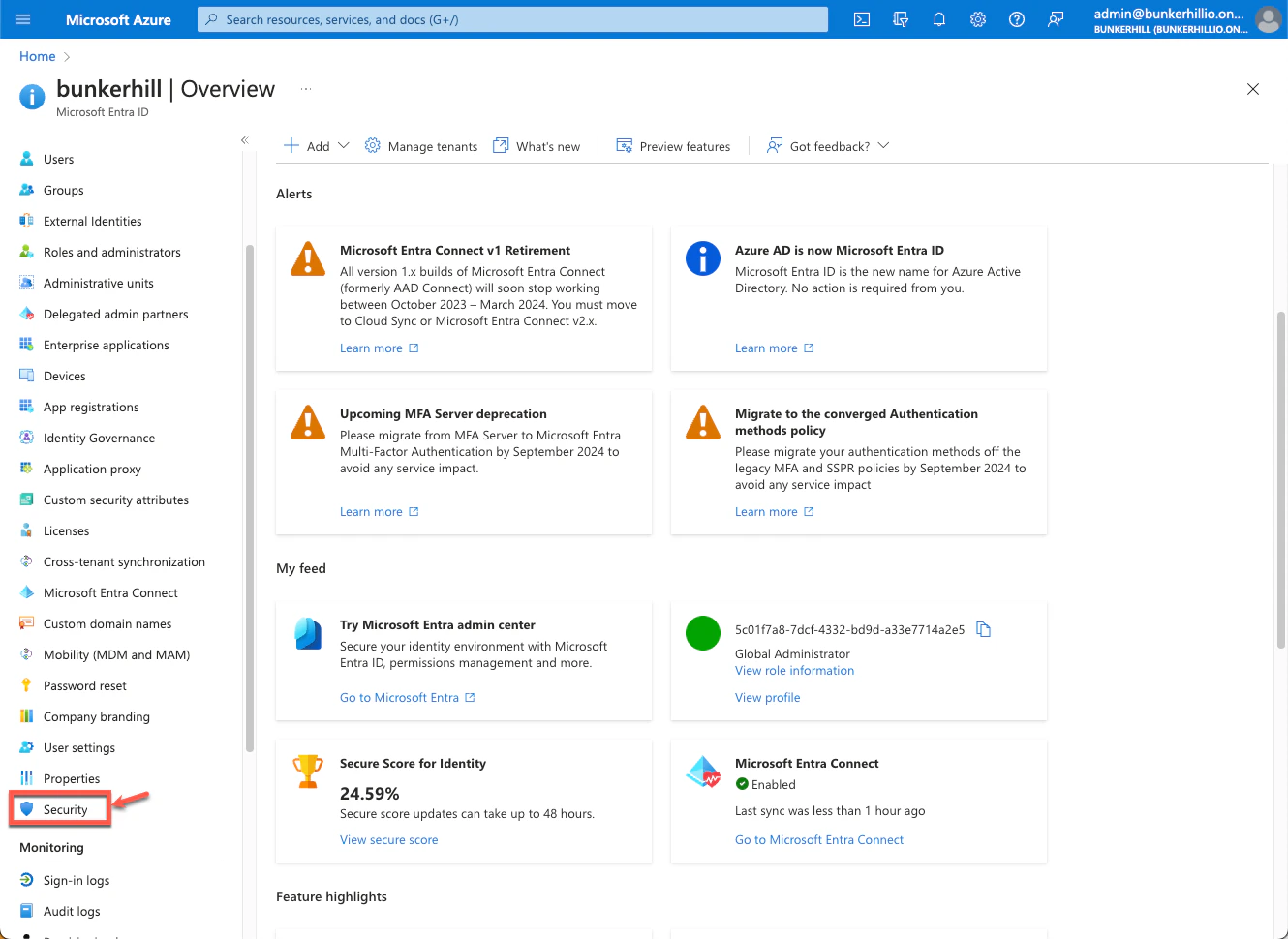
- Login to Microsoft Entra ID (Azure AD)
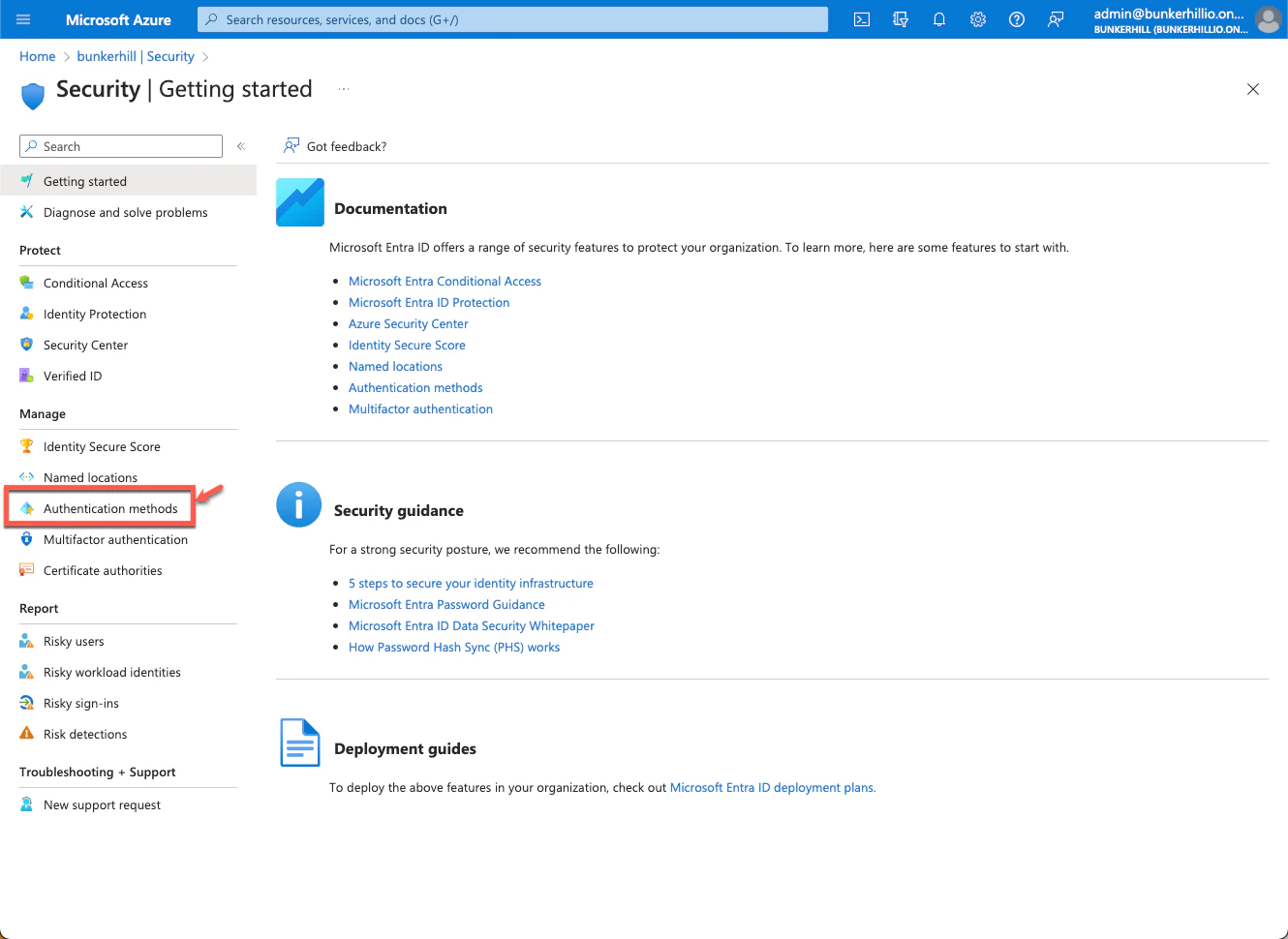
- Go to “Security”, then navigate to “Authentication Methods”
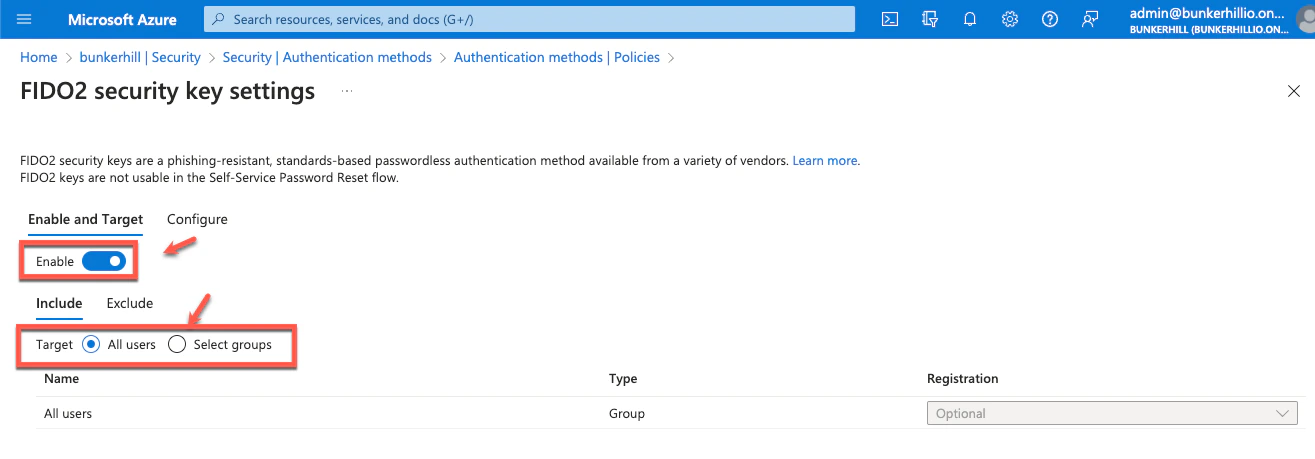
- Click on FIDO2 Security Keys and enable it for all users or selected users in a group and Save the settings
Note
If FIDO2 Security Keys are already enabled Configure FIDO2 security key settings.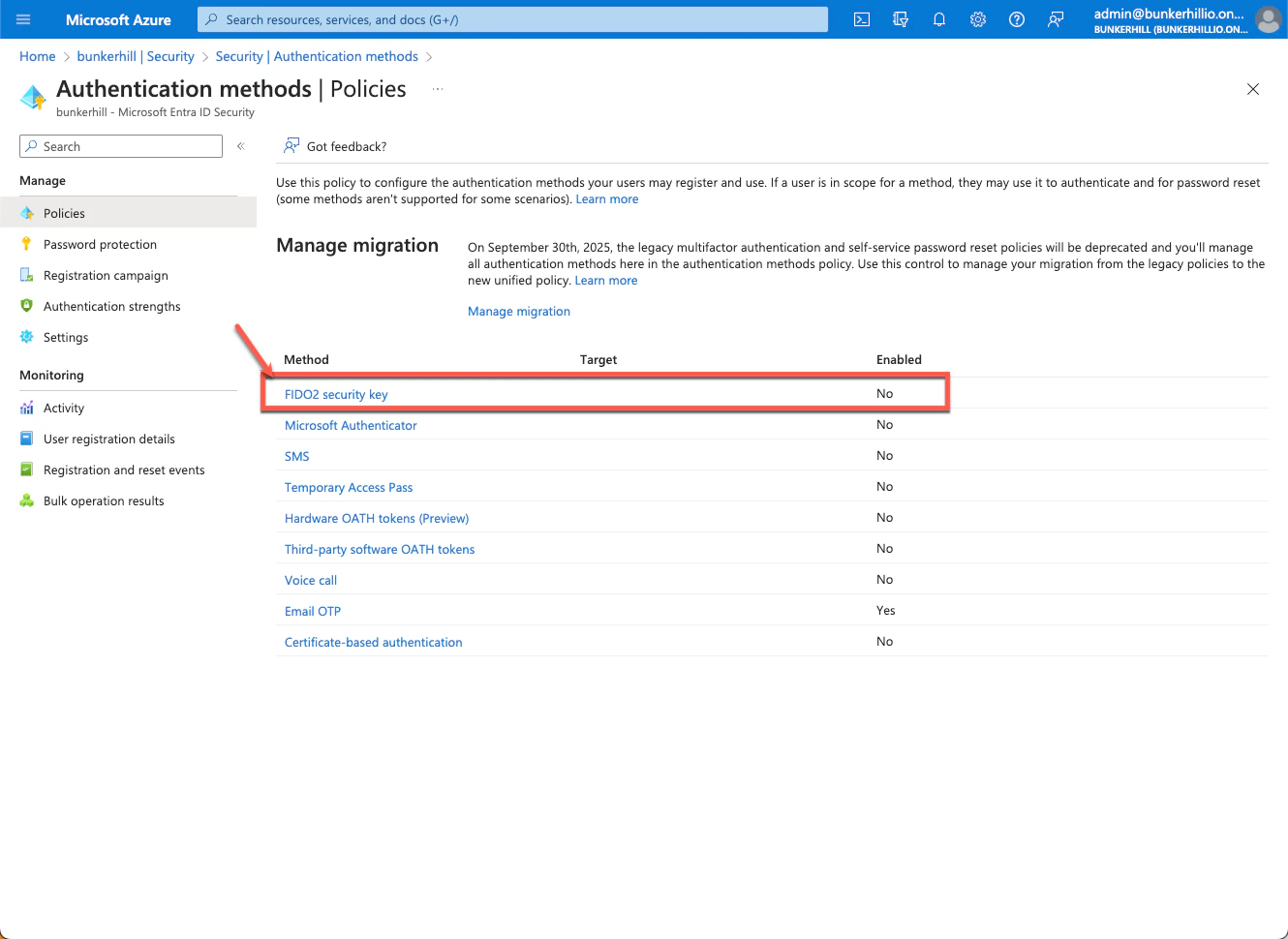
FIDO2 Security Keys Settings
- Go to “Configure” tab and set the following values:
- Allow self-service set up: Yes
- Enforce attestation: No
Attestation is designed to verify hardware manufacturing processes to prevent rogue hardware. TruU is a virtualized (does not require specialized hardware) solution that runs on top of Microsoft-verified hardware and does not require nor support hardware verification.
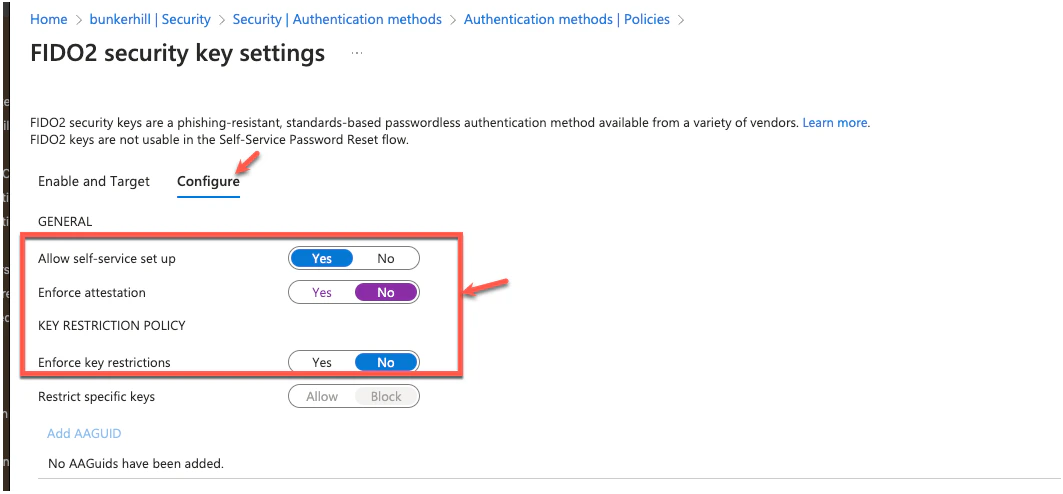
- Save the settings
Enable FIDO2 Login via Group Policy
https://docs.truu.ai/docs/enable-truu-fido2-login-using-windowsConfig File Requirements
In Line 21 of the Config File that you see below, you must edit the code to the following for Azure Joined Devices: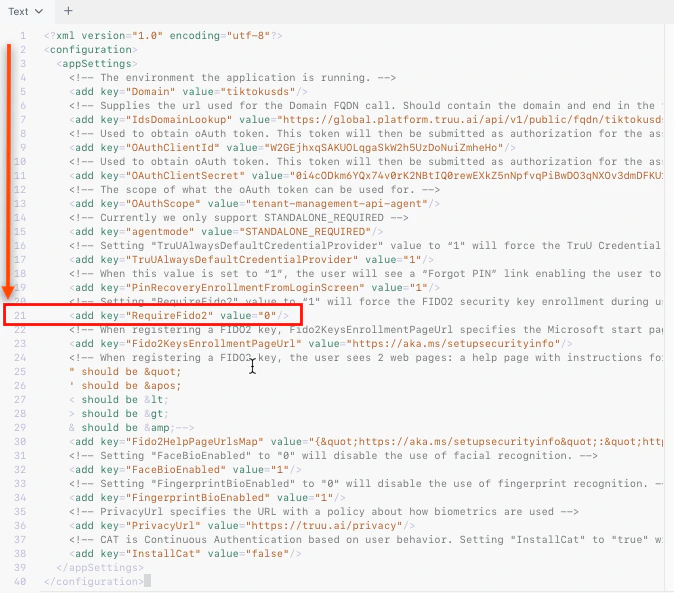
Networking and Firewall Requirements
First time Enrollment requires internet connectivity, Outbound traffic for the following URLs must be allowed from the client Windows device. Please make the necessary firewall changes.TruU URLs
https://global.platform.truu.ai https://customer.idp.id.truu.ai https://customer.cert.id.truu.aiMicrosoft URLs
The following endpoints are needed for registration and authentication: customer.microsoftonline.com customer.microsoftonline-p.com customer.msauth.net customer.msauthimages.net customer.msecnd.net customer.msftauth.net customer.msftauthimages.net customer.phonefactor.net enterpriseregistration.windows.net management.azure.com policykeyservice.dc.ad.msft.net secure.aadcdn.microsoftonline-p.comModalities Manual Install TruU - WA

