Documentation Index
Fetch the complete documentation index at: https://docs.truu.ai/llms.txt
Use this file to discover all available pages before exploring further.
Supported RADIUS Protocols
The TruU Cloud RADIUS adapter supports the Password Authentication Protocol (PAP) and the Client Handshake Authentication Protocol (CHAP). TECHNICAL NOTE: RADIUS clients may require a password from the end user. For instance, the GUI for VPN endpoint software may not let a user click to log in if a password field is empty. The RADIUS client will include this password when communicating with the TruU Cloud RADIUS adapter (the password will either be encrypted with the client/server shared secret or hashed depending on whether PAP or CHAP is used). TruU will always ignore the password. Users need not type a valid password. Whether or not a user is prompted for a password is a function of the RADIUS client, and cannot be influenced by the TruU adapter.Server Hardware Requirements
Customers are encouraged to consult server sizing guidelines from Red Hat. TruU recommends these minimums:- 2 vCPUs at 2+ GHz
- 8GB RAM
- 20GB Disk
Server Software Requirements
- RHEL 8
- Java 21
- TruU IDS v25.180 or higher
Networking Requirements
The server running the TruU Cloud RADIUS adapter must allow UDP traffic inbound on port 1812 from RADIUS clients.Installation Process
- Prepare the RHEL 8 server
- Install Java 21
- Test network connectivity from the RADIUS client(s)
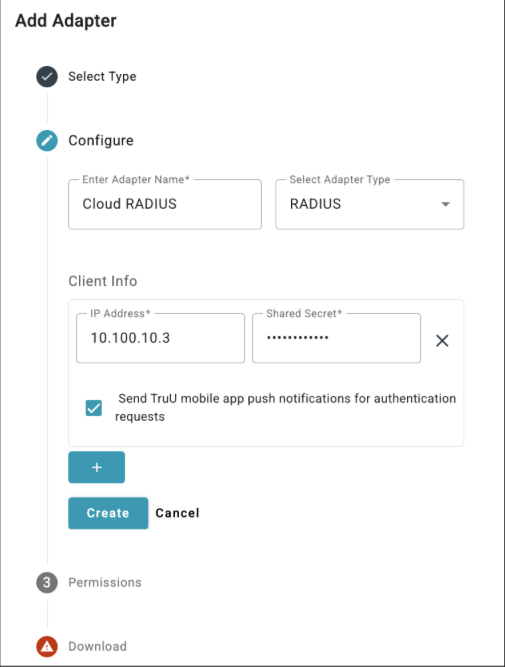
- Configure a RADIUS adapter in the TruU admin console and download the associated files
- Provide a meaningful name for the adapter
- Select RADIUS as the adapter type
- NOTE: the previous RADIUS solution which was built directly into the identity server has been renamed “Legacy RADIUS”Enter the IP address of your RADIUS client and the shared secret you wish to use between this client and the adapter
- Enable the Send TruU mobile app push notifications option if you want users to receive a push notification on their mobile phones running the TruU mobile app
- If this option is unchecked, users must open the TruU mobile app to look for an authentication request when using the RADIUS adapter
- Add additional client configurations as needed
- NOTE: you can add, modify, or remove clients from the adapter at any time by updating the adapter in the TruU admin console. The adapter will automatically apply these updates within 5 minutes of the changes being saved in the admin console.
- Download the RADIUS package truu-radius-server-version.zip and the accompanying truu-radius.ymlconfiguration file
- Upload truu-radius-server-version.zip and truu-radius.yml files to the RHEL 8 server
- Unzip the truu-radius-server-version.zip archive to extract the RPM installer
- Do this in the home folder of the user account used to connect to the server
- You should now have truu-radius.yml and truu-radius-version-1.el8.noarch.rpm together in the same home folder
- Install the RPM with the following command:
- Check the status of the truu-radius service with the following command. Confirm that the output indicates “Active: active (running)”:
- Test the integration
Installation Directory and Service Account
Installation of the RPM will create the following directory on the RHEL 8 server:Uninstallation
Use the following command to test if the truu-radius RPM is installed (sudo is not required):Architectural Overview
The TruU Cloud RADIUS adapter translates RADIUS authentication requests (UDP port 1812) to HTTPS REST API calls (TCP port 443). The REST API is managed by TruU identity servers, whether those are hosted in the TruU cloud or on a customer-managed network. The truu-radius.yml file contains the connection details that allow the adapter to communicate with the identity servers.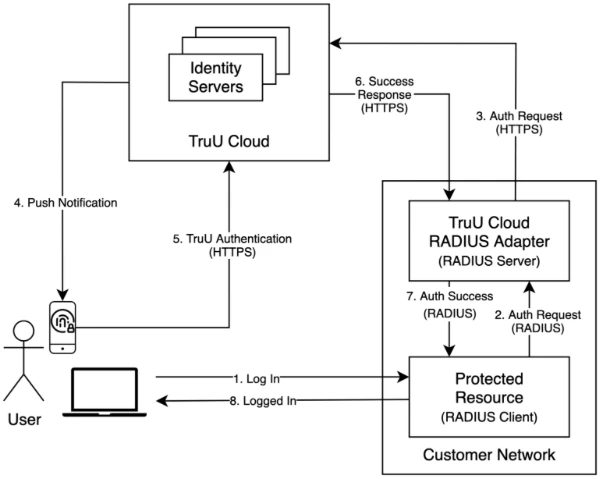
High Availability
Customers may configure one or more TruU Cloud RADIUS adapters to satisfy high availability needs. With multiple adapters, a customer has two HA deployment options:- Configure RADIUS clients to use multiple RADIUS servers
- Recall that an adapter acts as a RADIUS server
- Configure a network load balancer “in front of” multiple RHEL 8 servers, with each server running a TruU Cloud RADIUS adapter
- In this scenario, the network load balancer IP address is the address that you would use for the RADIUS server when configuring your RADIUS clients
Webhook Event Logging Adapter Setup Guide Other

