Documentation Index
Fetch the complete documentation index at: https://docs.truu.ai/llms.txt
Use this file to discover all available pages before exploring further.
Enable FIDO2 security key sign-in for Windows
Option One: Enable with Group Policy
- On the domain controller, open the Group Policy Management Console.
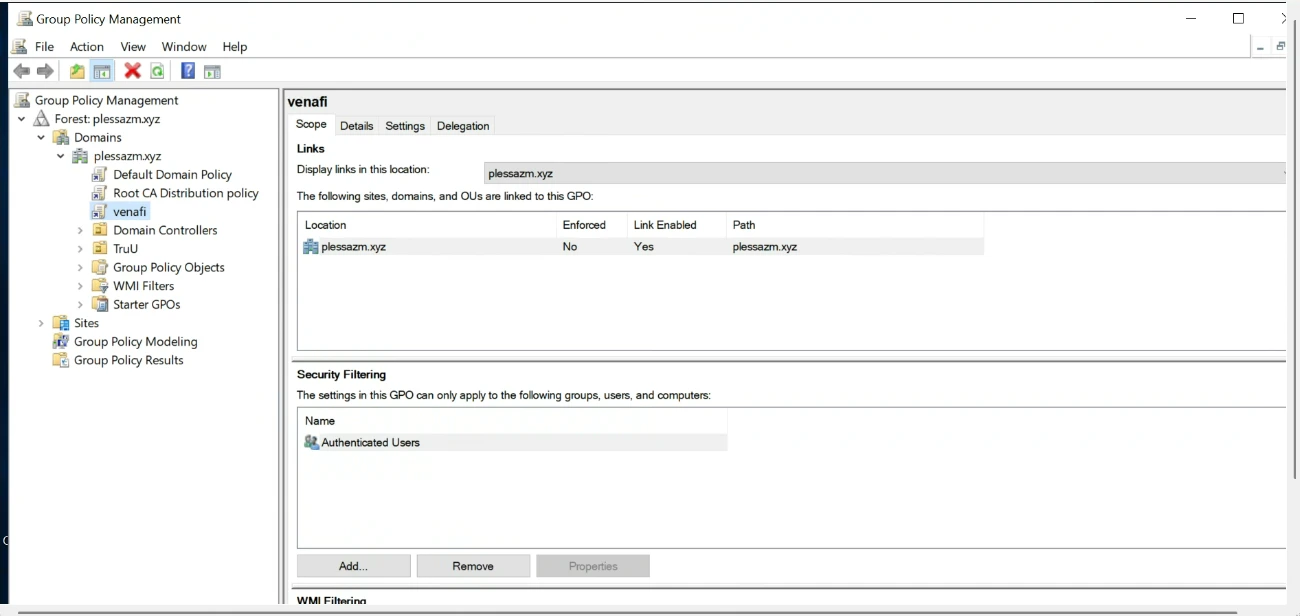
- Locate the policy you want to apply as a GPO to your Windows clients.
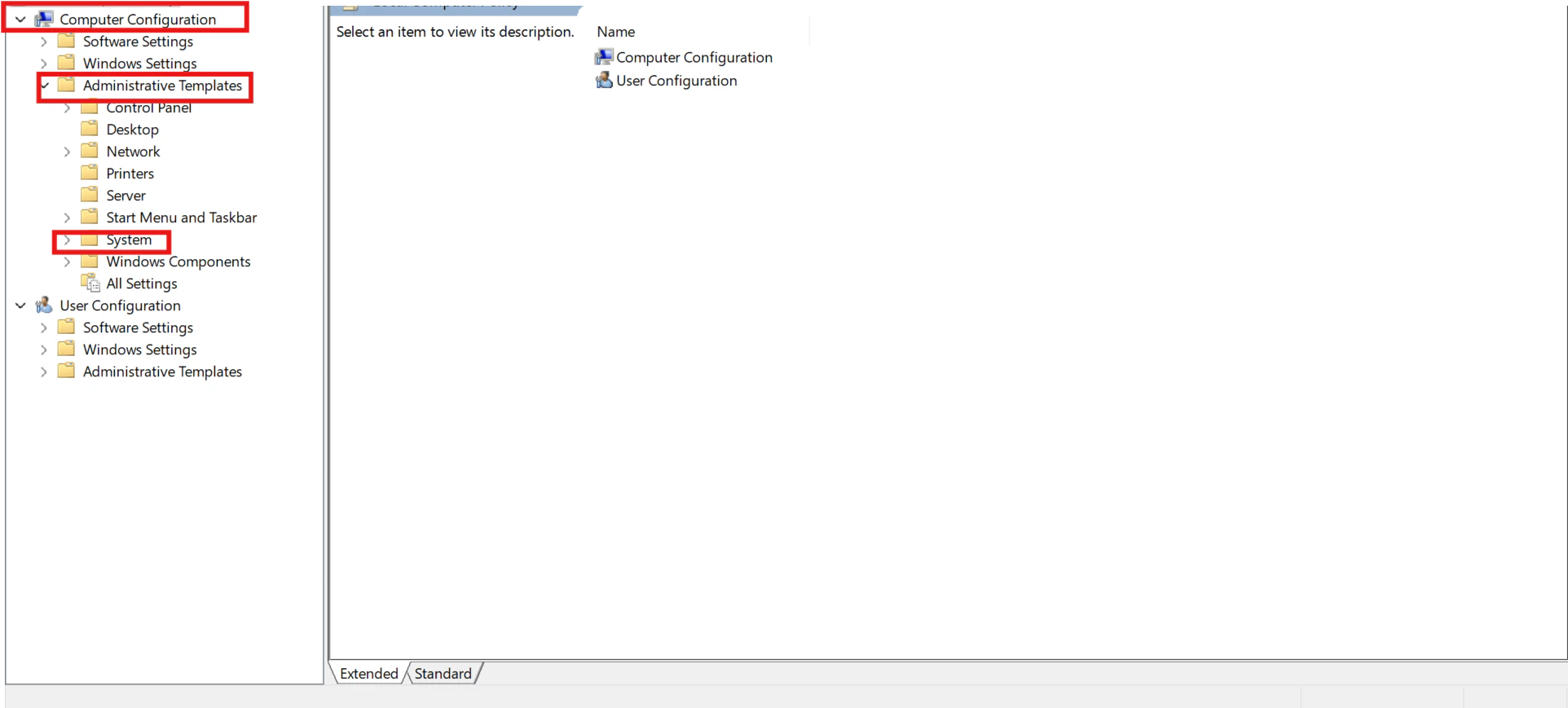
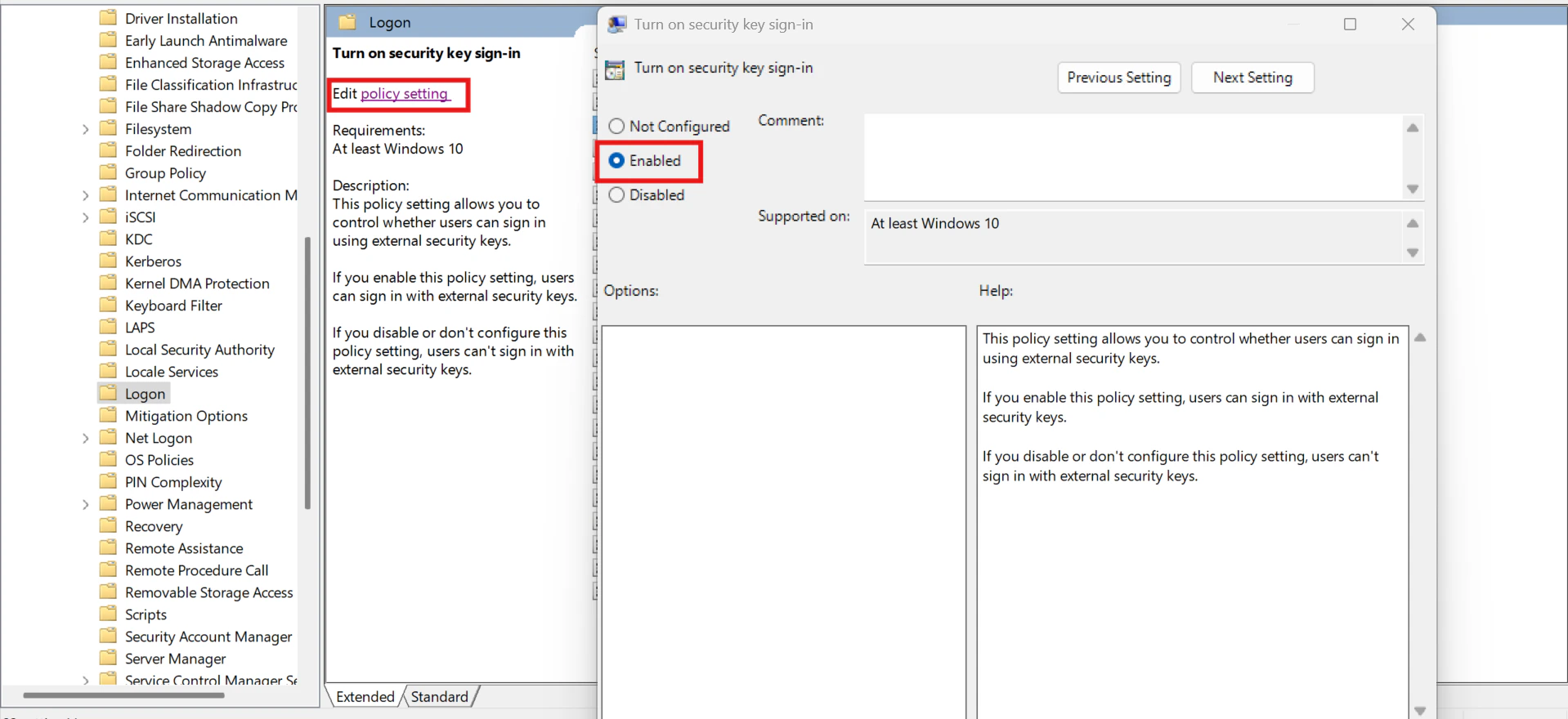
- Edit the policy, navigate to the Computer Configuration tab, then go to** Administrative Templates > System > Logon**, and select Turn on Security Key Sign-in.
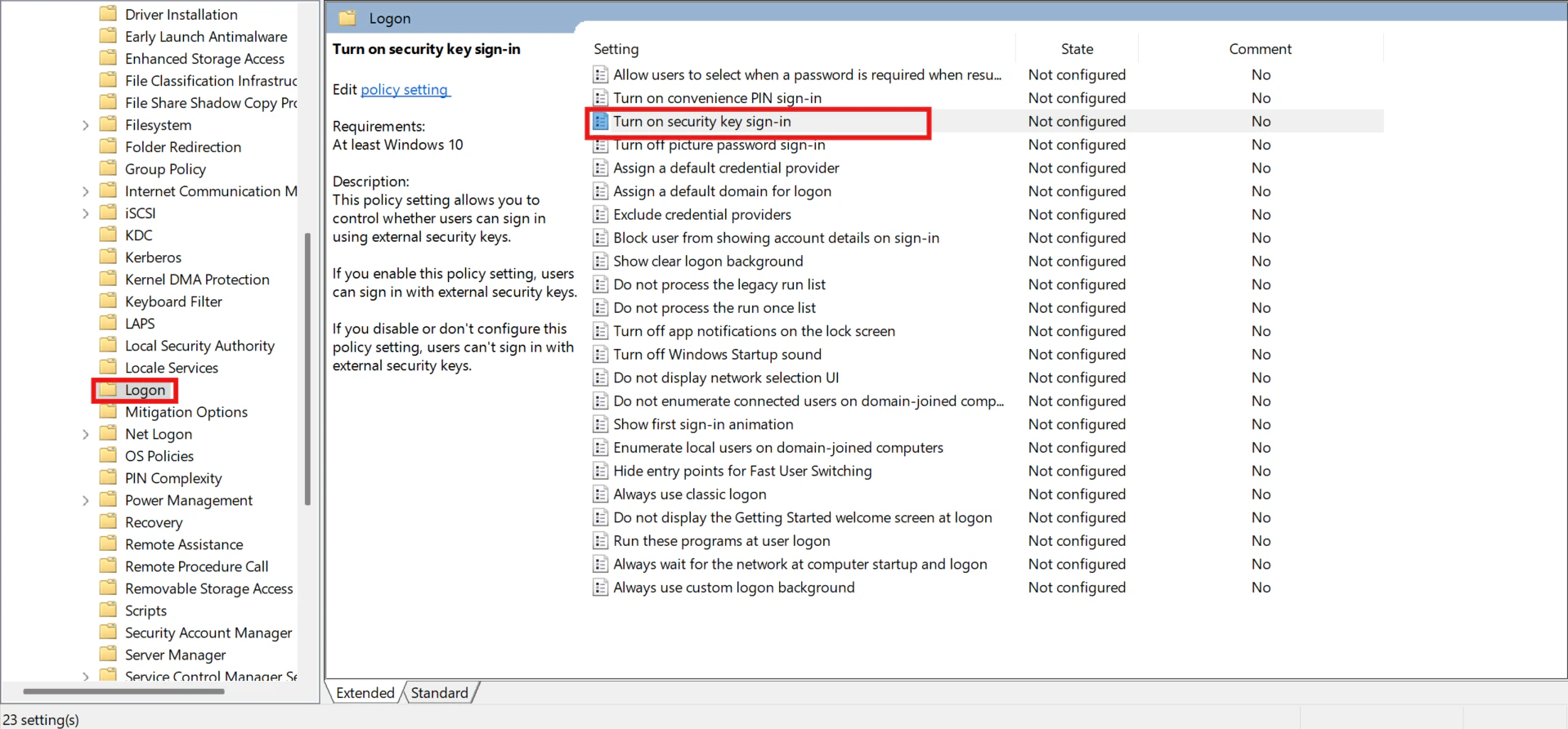
- Setting this policy to Enabled allows users to sign in using security keys.
- Setting this policy to Disabled or Not Configured disables security key sign-in for users.
Option Two: Add a Registry Key
- To enable security key sign-in using a registry key, deploy the following registry key to all your Windows clients using your preferred deployment tool.
Create a Device configuration profile
Option 1: Settings Catalog
- Sign in to the Microsoft Intune admin center
- Browse to Devices > Windows > Configuration profiles > Create new policy.
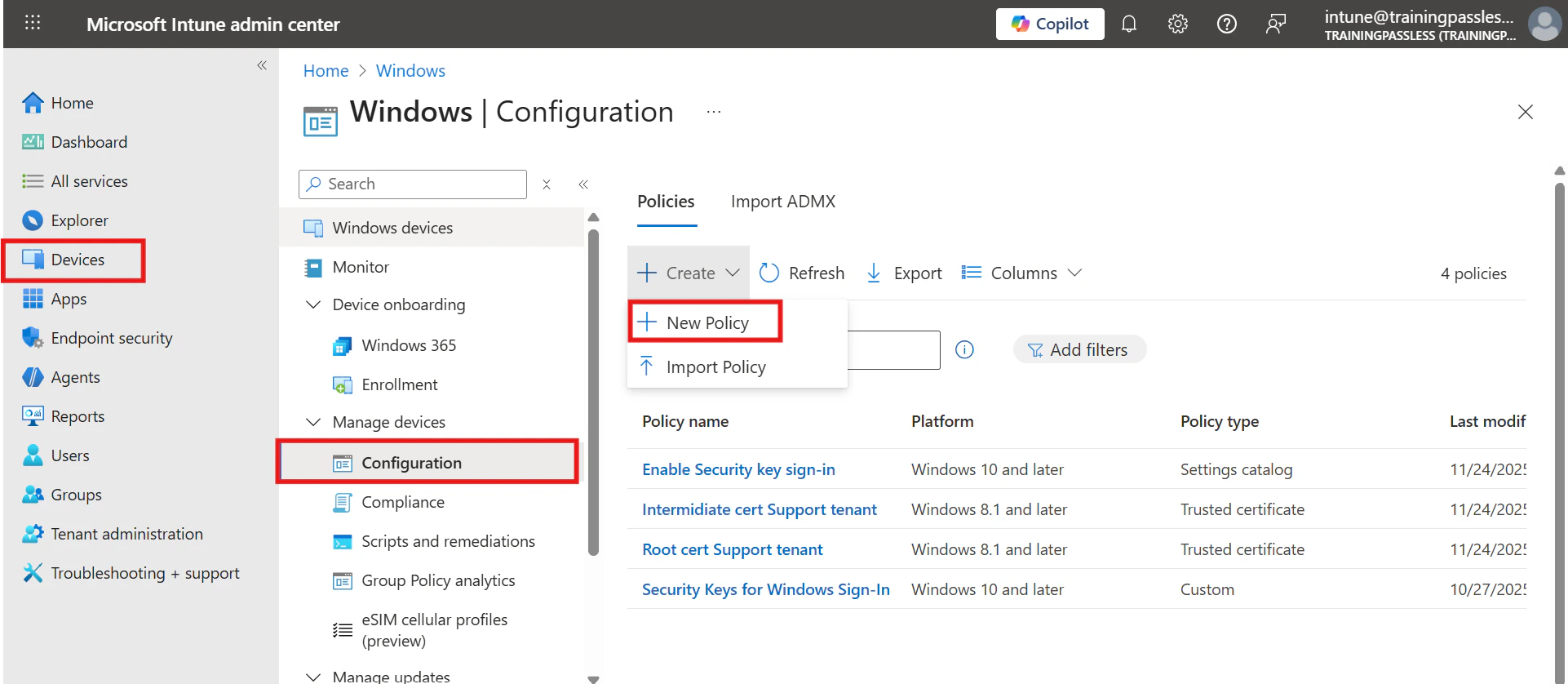
-
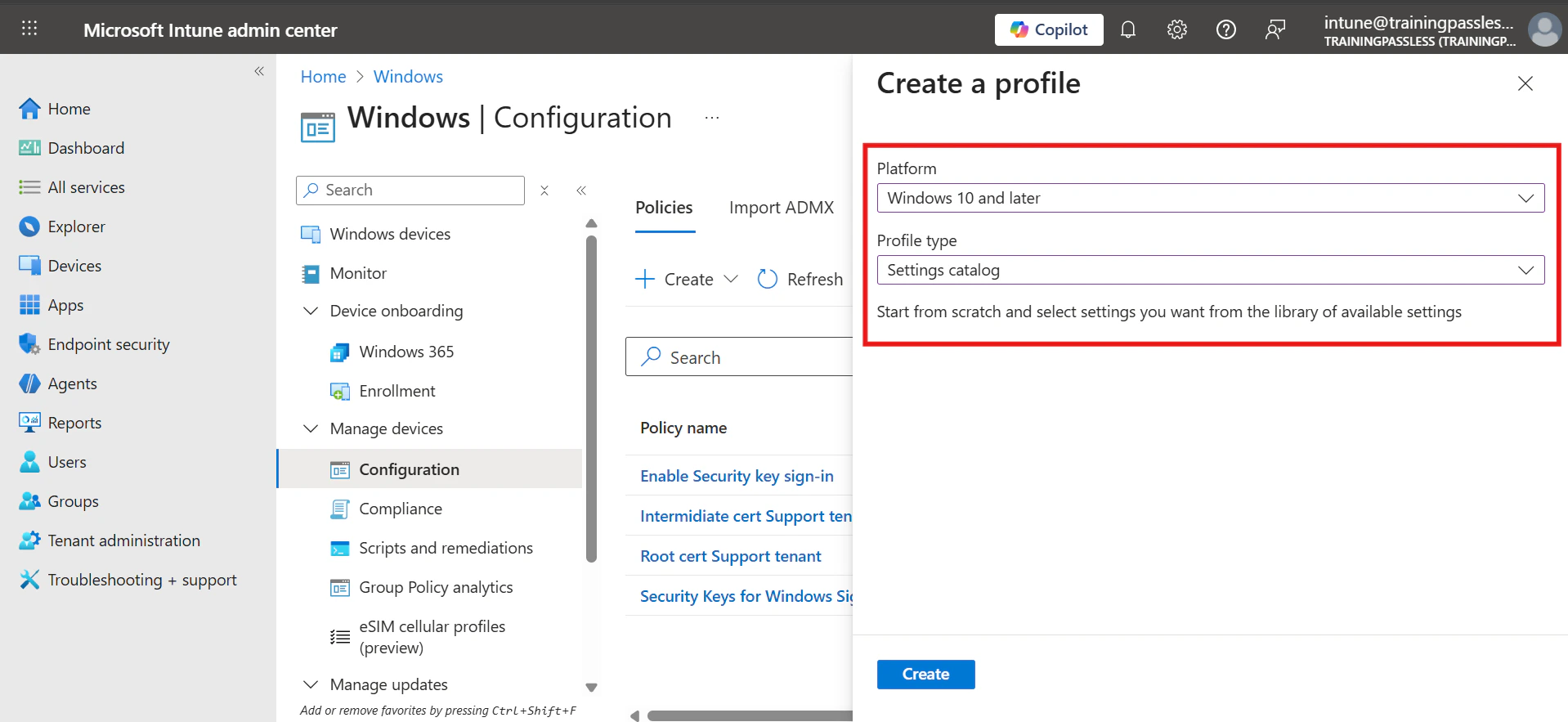
Configure the New Policy with the following settings:
- Platform: Windows 10 and later
- Profile type: Setting catalog
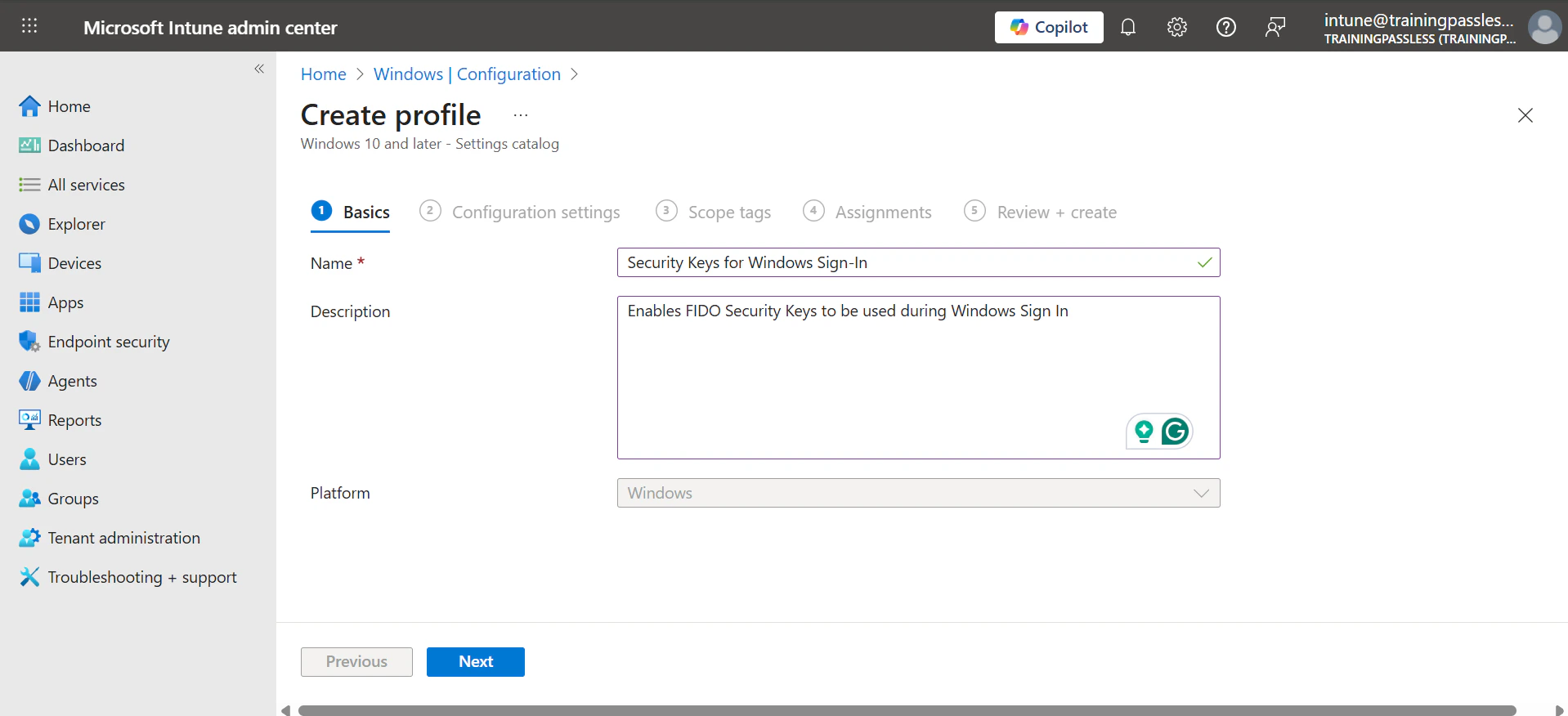
- Name: Security Keys for Windows Sign-In
- Description: Enables FIDO Security Keys to be used during Windows Sign In
-
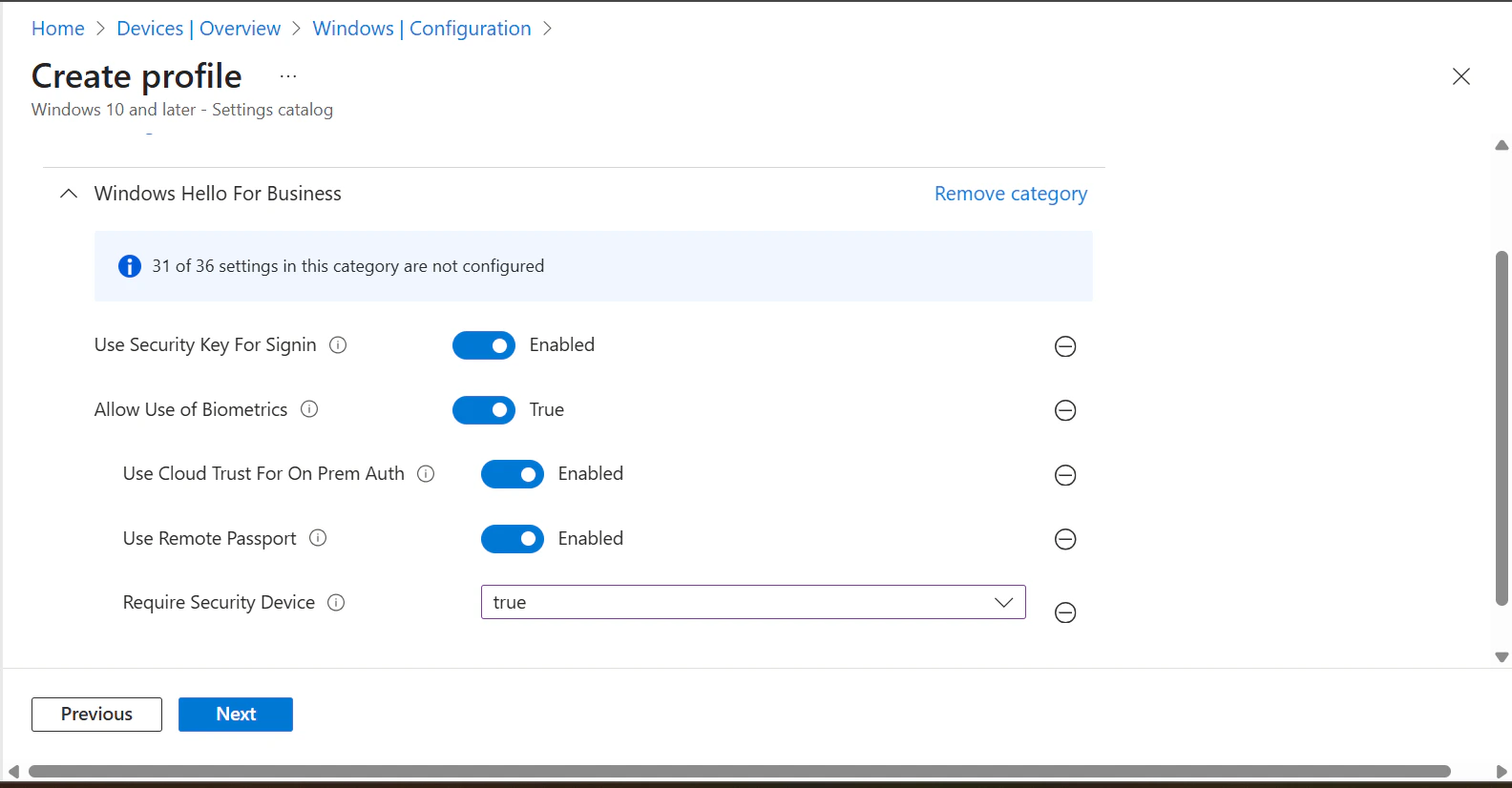
Under the Configuration settings> click onAdd settings > Select Windows Hello For Business and add below:
- Use Security Key For Sign-in
- Allow Use of Biometrics
- Use Cloud Trust For On-Prem Auth
- Use Remote Passport
- Require Security Device
- Assign the Policy to the Groups that should support TruU login.
Option 2: OMA-URI method
-
To target specific device groups to enable the credential provider, use the following custom settings via Intune:
- Platform: Windows 10 and later
- Profile type: Template and select Custom
- Name: Security Keys for Windows Sign-In
- Description: Enables FIDO Security Keys to be used during Windows Sign In
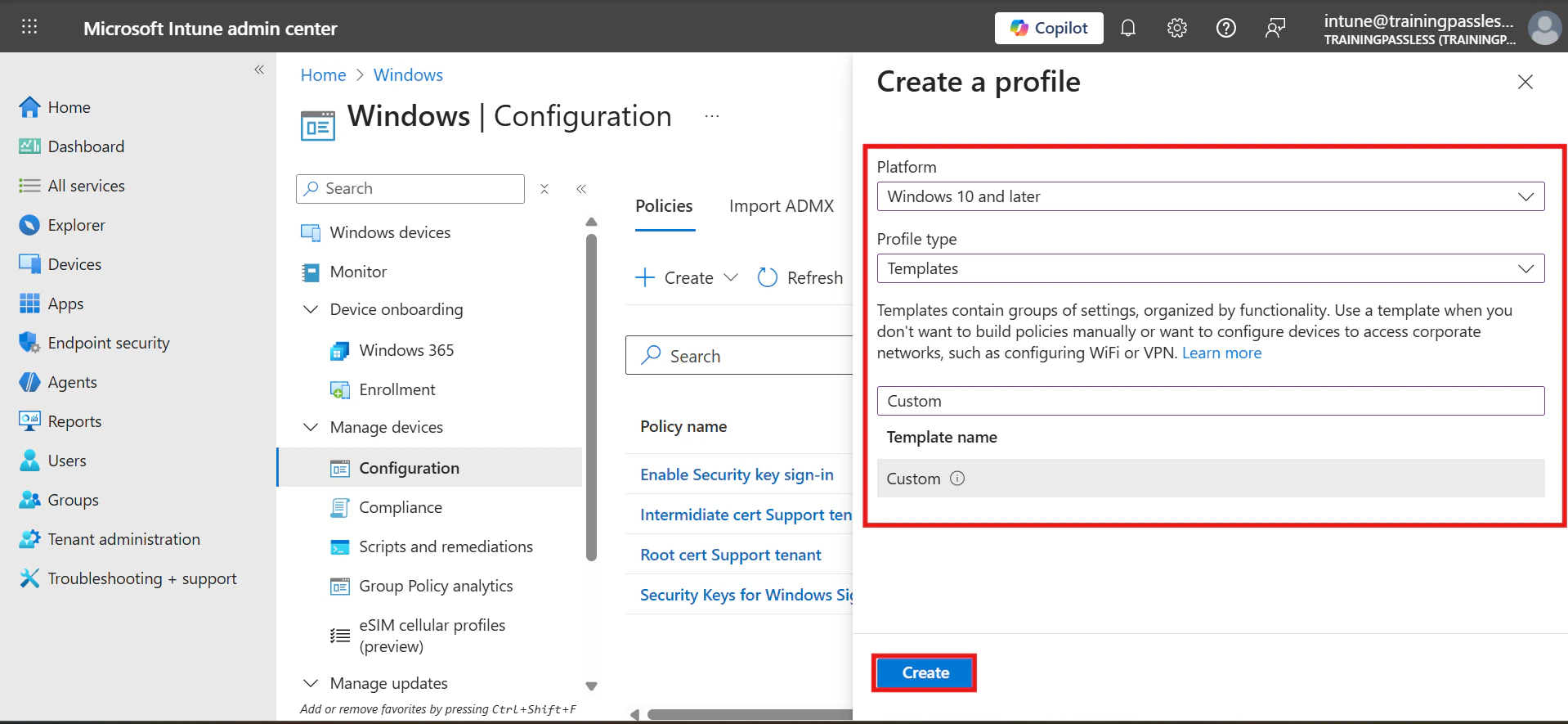
-
In the Configuration Settings tab, click on Add and enter the following
- Name: Turn on FIDO Security Keys for Windows Sign-In
- Description: (Optional)
- OMA-URI: ./Device/Vendor/MSFT/PassportForWork/SecurityKey/UseSecurityKeyForSignin
- Data Type: Integer
- Value: 1
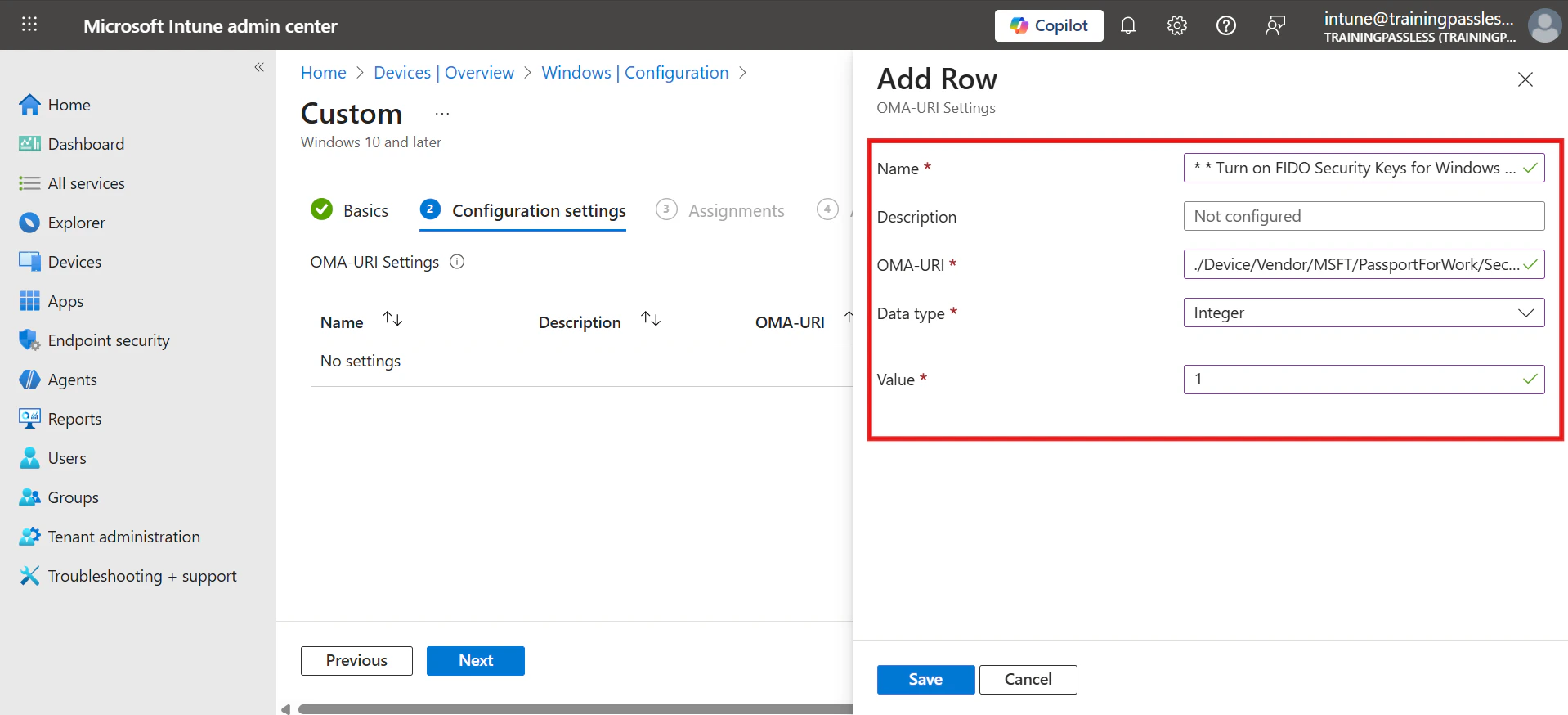
- Assign the Policy to the Groups that should support TruU login.
Enable Passkey (FIDO2) CyberArk Zero Touch PKI

