Date: March 30, 2024Documentation Index
Fetch the complete documentation index at: https://docs.truu.ai/llms.txt
Use this file to discover all available pages before exploring further.
Highlights
- Augmented Computer Data
- Users and Assets APIs
Enhancements
Augmented Computer Data
-
The to be released Desktop Authenticators will collect additional hardware data and share that information with the platform during enrollment and subsequent “heartbeats”. This enriches the context of event data, and the computers drill-down information available in the Admin Console. The enriched data includes:
- MAC Address
- IP Address
- Manufacturer
- Model
- Serial Number
- Processor
- BIOS Version (for macOS we present the EFI as the BIOS).
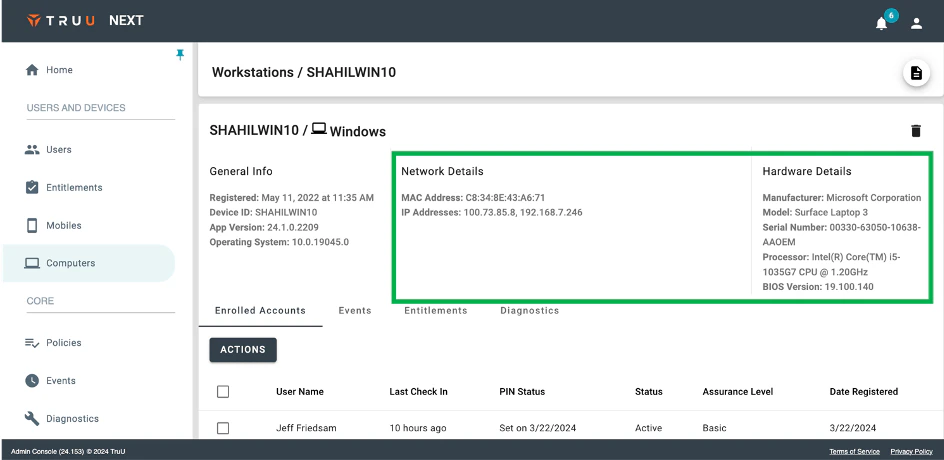
- NOTE: this data will be visible in the Admin Console with Identity Servers running 24.153 (or higher) and requires Windows Authenticator v24.1 (or higher) and Mac Authenticator v24.2 (or higher).
Users and Assets APIs
-
We’ve also updated our user management APIs to include two new data APIs to query the platform for information about:
- Users: The Users API returns users and their enrolled devices.
- Assets: The Assets API returns workstations and the enrolled accounts on those workstations (including user information).
- Refer to the User Management API Guide in the online help for full details on how to use the APIs.
Bug Fixes
-
We have improved experience for SSO deep-link failures on Android. Improvements for this fall-back scenario are as follows:
- Users who have successfully authenticated with that browser in the past, and where the browser supports cookies, will get a push notification to authenticate.
- If the browser does not support cookies, but the IdP provides a login hint, the user will see an action card to approve when they open the app.
- For all other cases, the user will see a more streamlined flow including one less screen and reduced text instructions for how to proceed.
- NOTE: this fix requires 24.153 (or higher) Identity Servers.
- We have fixed an issue which prevented the name of some card readers from appearing as the Target in the Events page for some physical access events.
- We have fixed an issue where deleting a FIDO hardware token from the User Portal would not create a de-registration event in the Admin Console.
- We have fixed an issue which caused some event data to appear with dates in the future.
- We have fixed an issue where changing a device assurance level through the Admin Console and identified the method of verification as “Video Conference” would result in the device appearing with the assurance level of “Certified” where it should have been “Trusted”.
Known Issues
| Ticket Number | Component | Summary |
|---|---|---|
| PLAT-9447 | Misc. | Unfriendly error message when Device is below Minimum Device Assurance Level for Application SSO |
| PLAT-9359 | Admin Console | The view of devices does not get updated immediately when dormant settings are modified. If the Admin changes the “Stale Device Handling” configuration under “Settings > Security”, the status for devices (Active / Dormant) may not be accurate for up to 15 minutes as the status is cached and updated every 15 minutes. |
| PLAT-9302 | Admin Console | In rare instances, Admin Console may fail to load. If this happens, refresh the page |
| PLAT-9891 | PIN Reset | If a PIN profile is updated from not requiring PIN rotation to require PIN rotation, already enrolled devices will not honor that policy. Workaround: manually set the enrolled device(s) to require a PIN change. This will force the user to change their PIN on next check-in, and updated PIN profile will be used moving forward. |
| WA-18595 | Policies | Failed policy evaluation events from iOS devices appear twice in the Events table. |
| PLAT-10730 | Event Logging | IP address and location information are missing in some events in the Events table. |
PLAT 24.155 Release Notes PLAT 24.152 Release Notes

